
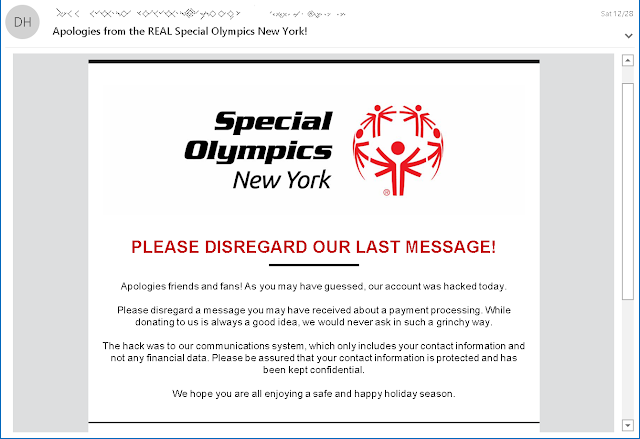
Promptly as the issue surfaced a notification was sent by the nonprofit to reveal the security episode to the people influenced, asking the donors to dismiss the last message received and clarifying that the hack just affected the "communications system" that stores just contact information and no financial information.
"As you may have noticed, our email server was temporarily hacked. We have fixed the problem and send our sincerest apologies," email notification from Special Olympics New York told donors.
The phishing messages conveyed by the attackers were 'camouflaged' as an alert of an approaching donation transaction that would consequently debit $1, 942, 49 from the target's account within two hours.
Utilizing such a brief span outline enabled the phishers to initiate a 'sense of urgency' intended to make the Special Olympics NY donors click on one of the two installed hyperlinks, links that would, as far as anyone knows, divert them to a PDF rendition of the transaction statement.
The phishing email used a Constant Contact tracking URL that redirected to the attackers' landing page. This page has since been brought down, however, it was in all likelihood used to steal the donors' credit card subtleties.
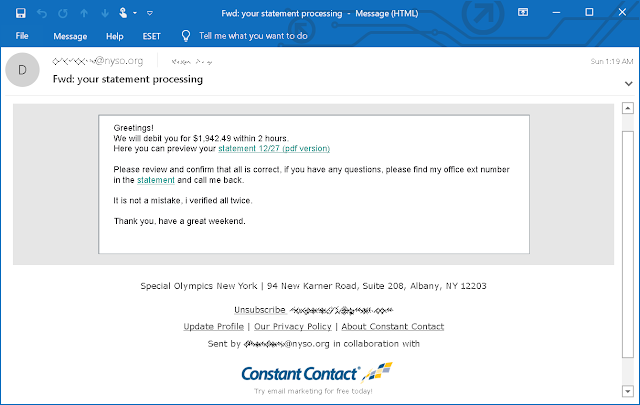
"Please review and confirm that all is correct if you have any questions, please find my office ext number in the statement and call me back," the phishing emails said. "It is not a mistake, I verified all twice. Thank you, have a great weekend."
Shockingly so, this isn't the first, historically speaking, episode where such a ‘mishappening’ was recorded, as the Tokyo 2020 Summer Olympics staff additionally gave an admonition cautioning of a phishing campaign that conveyed emails intended to look like they had originated from the Tokyo Organizing Committee of the Olympic and Paralympic Games (Tokyo 2020).
And additionally said that the malignant emails probably diverted the beneficiaries to landing phishing sites or tainted the victim's PCs with malware whenever opened.
Read more https://www.ehackingnews.com/2020/01/email-server-of-special-olympics-of-new.html

